Amid intense backlash, the head of the American Diabetes Association posted a video Wednesday apologizing for the organization's decision on Friday to forcefully remove five leading diabetes scientists from the association's annual meeting.
The scientists were ejected for handing out copies of an April editorial—published in the ADA's own journal Diabetes Care—that sharply criticizes the Trump administration for the damage and destruction it's wreaking on biomedical research. The five scientists included Steven Kahn, professor of medicine at the University of Washington, who is the editor-in-chief of Diabetes Care and a co-author of the editorial. It also included former ADA President Desmond Schatz of the University of Florida.
The scientists were distributing the editorial outside the conference's opening speech, which was originally scheduled to be given by Jay Bhattacharya, head of the National Institutes of Health under Trump. Bhattacharya canceled at the last minute, and senior NIH official Rick Woychik took his place.
Within minutes of beginning to hand out the editorial, police reportedly escorted the scientists out of the conference, which was held in New Orleans. The police reportedly shoved at least one scientist, took all of their conference badges, and threatened to arrest them if they tried to return. Louisiana State Police later told media that they acted at the request of the ADA. The ADA subsequently barred the five scientists from the rest of the conference.
In the video Wednesday, ADA CEO Charles Henderson personally apologized to the five scientists, including Aaron Kelly, pediatrics professor at the University of Minnesota; Justin Ryder of Northwestern University; and Irl Hirsch, also of the University of Washington, in addition to Kahn and Schatz.
"What transpired is not reflective of who I am, the values I hold, or the way I was raised," Henderson said. "I will work hard to bring our community back together to build on the progress we have collectively made for those affected by diabetes."
While the ousting immediately stunned and outraged members of the diabetes research community, Henderson's video is in sharp contrast to the ADA's series of statements over the past several days that tried to justify the decision. At first, a media team for the ADA told MedPage Today that "these attendees were escorted out by our onsite event security because they demonstrated behavior not consistent with this code of conduct" for the conference.
"Fatuous nonsense"
In an email to ADA members Saturday, the association said the scientists were removed because they didn't have prior approval to distribute material at the conference and that it was "not because of the viewpoints expressed in those materials," according to reporting from Science.
In a statement Sunday, the organization, which is a nonprofit, said it removed the scientists because it was complying with federal regulations for 501(c)(3) nonprofit, which requires "maintaining a strictly nonpartisan environment at all organizational events and functions while engaging across party affiliations to advance our mission." However, the federal regulations do not restrict leaders of organizations from sharing political views in a personal capacity or from speaking on important public policy issues.
News and video of the incident took off on social media, drawing condemnation and driving a traffic spike to the editorial. Several ADA leaders have resigned amid the backlash. A fiery letter signed by more than 40 ADA officials blasted the decision as "outrageous" and the justifications as "unpersuasive" and "fatuous nonsense." The community is "overwhelmingly repulsed by the way this unfortunate event has occurred and been excused and justified by the Association leadership," the leaders wrote. They demanded "an immediate and unconditional public apology," as well as a review of the incident.
An open letter to the ADA, titled "Shame on You," similarly called for an apology. The attacks from the Trump administration are "bad enough, but the seeming endorsement by the ADA of the current administration's approach to science and of its attacks on freedom of speech is unconscionable." The letter has gathered over 6,500 signatures at the time of publication.
In addition to apologizing to the five ejected scientists, Henderson apologized to the community as a whole, saying that the ADA would commission a "thorough independent review of the events that occurred as well as the policies, procedures, and decision-making process that guided our actions."
"We want to make sure that such incidents do not reoccur," he said.





 Introducing the new Shortcut Guide
Introducing the new Shortcut Guide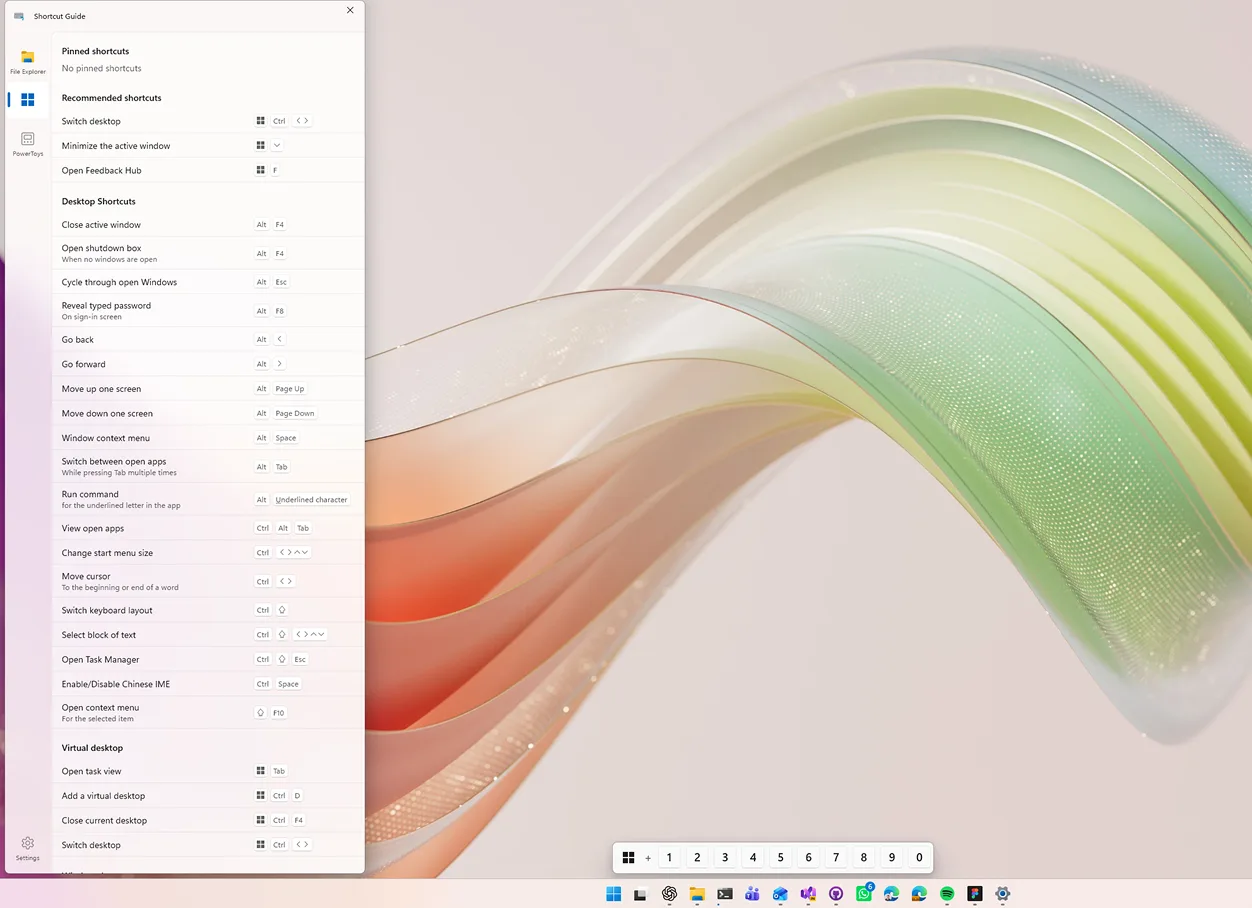
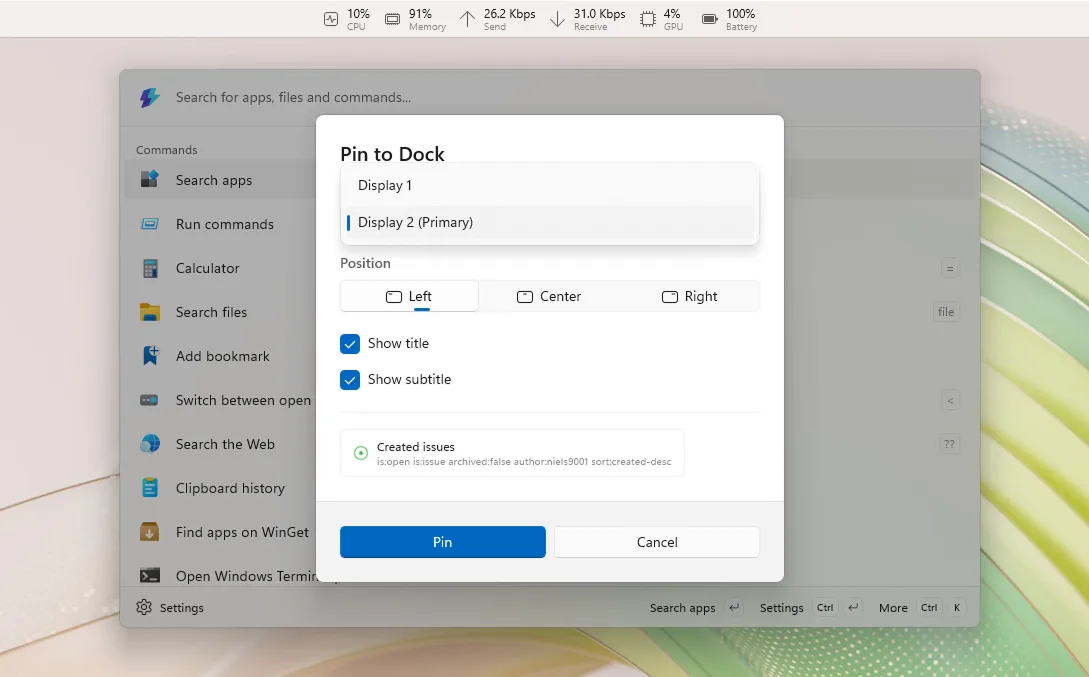
 Command Palette: new Extension Gallery, and multi-monitor Dock (and more!)
Command Palette: new Extension Gallery, and multi-monitor Dock (and more!)
 Power Display improvements
Power Display improvements ZoomIt: webcam capture and recording improvements
ZoomIt: webcam capture and recording improvements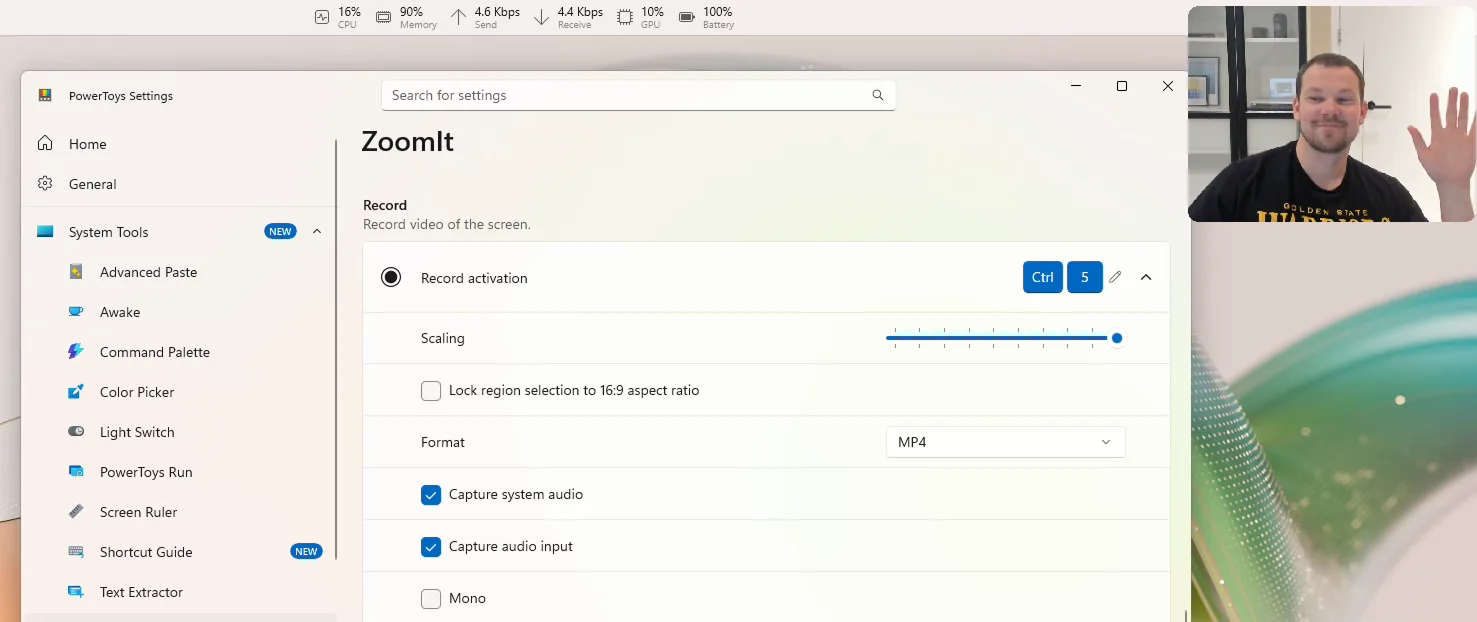
 Foundations and platform improvements
Foundations and platform improvements Other notable changes
Other notable changes Big thanks to the community
Big thanks to the community Useful links
Useful links